Table of Contents
Developing a complex IoT product for a high-reliability industry like medical, aerospace, or industrial automation means security is not an add-on; it is a fundamental design requirement. A single vulnerability can lead to catastrophic safety failures, costly recalls, regulatory penalties, and a complete loss of market trust. For the engineering VP, program manager, or technical lead responsible for delivery, the challenge is implementing a robust security posture without derailing timelines or budgets.
This article provides an actionable framework of the most critical IoT security best practices for those building connected hardware products where failure is not an option. Moving beyond generic advice, it offers specific implementation criteria, tradeoffs, and failure modes relevant to high-stakes environments. This guide applies when you are in the architecture, development, or pre-production stages of a regulated or mission-critical IoT device.
- Architect for Resilience: Explore foundational practices like secure boot and hardware-rooted trust.
- Protect Data Everywhere: Dive into end-to-end encryption for data in transit and at rest.
- Maintain Control Post-Launch: Cover secure OTA updates, monitoring, and lifecycle management.
We will focus on building a defensible system that is secure by design, from the first prototype to mass production and beyond, by framing each practice as a series of engineering decisions with clear risks and outcomes.
1. Secure Boot and Firmware Integrity Verification
At the moment an IoT device powers on, it is at its most vulnerable. Secure boot creates a chain of trust starting from the very first line of code executed, ensuring that only authenticated and authorized firmware runs on the device. It cryptographically verifies the bootloader and subsequent software components, like the kernel, before they are loaded. This process is a fundamental defense against attackers who aim to install malicious code, gain persistent access, or tamper with device functionality at the lowest level.
This first line of defense is one of the most important IoT security best practices for high-reliability and regulated products. For example, a pacemaker running compromised firmware could have fatal consequences, and an industrial robot with a tampered bootloader could cause serious injury or production-line failure. By validating every stage of the boot sequence, you build a trusted computing base that all other security measures can rely on.
Key Insight: Secure boot isn’t just a feature; it’s the architectural foundation for device integrity. It answers the critical question: “Is the software running on my hardware exactly what I intended to run, and nothing else?” Without it, all higher-level security controls can be bypassed.
Implementation Steps and Considerations
- Establish a Robust Key Management System: Use a hardware security module (HSM) or a cloud-based KMS (like AWS KMS or Azure Key Vault) from the project’s start to manage the private keys used for signing firmware. These keys are the cornerstone of your trust model.
- Implement Measured Boot: Complement secure boot with measured boot. A Trusted Platform Module (TPM) can measure (hash) each component as it loads and store these values securely. This log allows a remote server to attest that the device booted with the correct, untampered software.
- Design Resilient Update Mechanisms: Your secure over-the-air (OTA) update process must include anti-rollback protection to prevent attackers from downgrading to a version with known vulnerabilities.
- Document the Chain of Trust: For compliance and auditing, especially in medical or aerospace, you must document the entire chain of trust, from the hardware root to the application layer. This is a key part of demonstrating how you build a secure embedded system.
Trade-Offs and Failure Modes
Secure boot is not without its challenges. The primary trade-off is increased complexity in both development and manufacturing. Key provisioning and secure flashing add steps to the production line that must be carefully managed. A lost signing key or a bricked device in the field due to a failed boot validation can be costly, making recovery planning essential. For cost-sensitive consumer devices, the expense of a TPM or a more complex SoC might be prohibitive.
2. End-to-End Encryption and Secure Communication Protocols
Once an IoT device is running trusted code, its next task is often to communicate. End-to-end encryption (E2E) ensures that data sent between devices, gateways, and cloud platforms remains confidential and tamper-proof. It achieves this by encrypting data at the source and decrypting it only at the final, intended destination. This is a critical IoT security best practice for protecting sensitive information such as medical records, proprietary industrial data, and safety-critical aerospace commands where interception could lead to regulatory violations, operational failure, or physical harm.
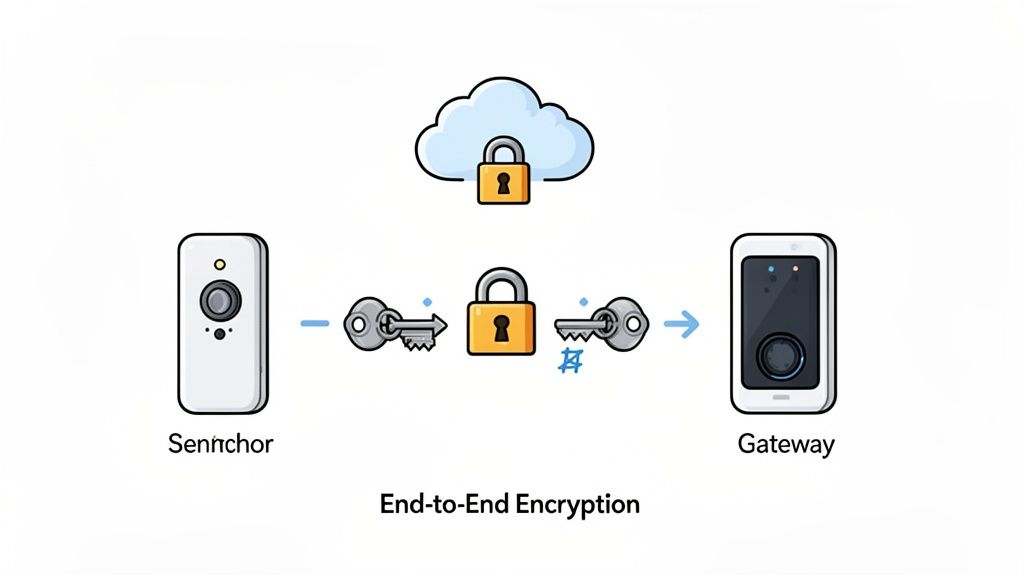
Unlike simple transport-layer security, which might terminate at a gateway, true E2E encryption protects data across its entire journey. For example, a glucose monitor’s data remains unreadable to any intermediate network hops as it travels to a cloud service for analysis. Similarly, an industrial robot controller receiving commands from a central server can be sure those commands haven’t been altered in transit by a malicious actor on the local network. This level of protection is mandated by frameworks like the NIST Cybersecurity Framework and is a core feature of platforms such as AWS IoT and Azure IoT Hub.
Key Insight: Securing the data transport layer (like with TLS) is necessary but not sufficient. End-to-end encryption provides a defense-in-depth security control that assumes other network layers could be compromised, protecting the data itself regardless of the path it takes.
Implementation Steps and Considerations
- Implement Mutual TLS (mTLS): Require both the device and the server to present and validate certificates for mutual authentication. This prevents unauthorized devices from connecting to your cloud and stops devices from sending data to imposter servers.
- Use Certificate Pinning: To defend against man-in-the-middle attacks resulting from a compromised Certificate Authority (CA), pin the server’s public key or certificate within the device firmware. This ensures the device will only connect to your known, authorized endpoint.
- Automate Certificate Lifecycle Management: Certificates expire. Implement an automated process using protocols like ACME or services from your cloud provider to handle certificate issuance, renewal, and revocation without manual intervention, preventing service outages.
- Choose Appropriate Protocols: Select communication protocols based on device constraints. Use TLS for standard TCP-based protocols like MQTT. For constrained, low-power devices using UDP-based protocols like CoAP, implement DTLS (Datagram Transport Layer Security). Proper protocol selection is a key aspect of designing effective Wi-Fi for IoT applications.
Trade-Offs and Failure Modes
The primary trade-off with strong encryption is performance and resource overhead. Cryptographic operations consume CPU cycles and power, which can be significant on battery-powered, resource-constrained microcontrollers. This overhead must be tested during prototyping. Additionally, managing a fleet’s worth of unique certificates introduces complexity into manufacturing and operations. If a private key on a device is compromised, it can be used to impersonate that device, making secure key storage (using a secure element or HSM) a critical dependency. Misconfigured certificate validation can also lead to widespread, hard-to-diagnose connectivity failures in the field.
3. Device Authentication and Identity Management
Knowing what is connected to your network is a core principle of security. Strong device authentication ensures that every connected device is legitimate, authorized, and identifiable. It uses unique cryptographic identities, such as certificates or keys, to prevent unauthorized or rogue devices from accessing networks, APIs, and data. Without this, an attacker could spoof a legitimate device to inject malicious commands or exfiltrate sensitive information, a critical failure for any connected system.
This practice is fundamental in environments where a single unauthorized device can create significant risk. Consider an industrial control system where a fake sensor broadcasts erroneous data, causing a production line to halt or operate unsafely. Similarly, in a hospital, a rogue device masquerading as an infusion pump could disrupt a medical network or access patient data, violating HIPAA and endangering lives. Secure identity is the passport that allows devices to participate in a trusted ecosystem.
Key Insight: Device identity isn’t just for access control; it’s the basis for the entire device lifecycle. It enables secure onboarding, updates, telemetry, role-based permissions, and eventual decommissioning. It answers the question: “Can I prove this device is what it claims to be, and can I trust it?”
Implementation Steps and Considerations
- Establish Unique, Unclonable Identities: Provision every device with a unique cryptographic identity at manufacturing time. Services like Azure DPS or AWS IoT Fleet Provisioning can automate this, but the key material must be protected. Storing private keys in a hardware-backed secure element (like a TPM or secure enclave) is a critical step to prevent extraction.
- Implement Mutual Authentication: Configure connections so that both the device and the server must prove their identities to each other (mutual TLS). This prevents man-in-the-middle attacks where a fake server could intercept device communications.
- Plan for Certificate Lifecycle Management (CLM): Certificates expire. An automated CLM system is necessary to handle the renewal and rotation of credentials without manual intervention, which is impossible at scale. This system must also support immediate revocation for any device that is suspected of being compromised.
- Tie Identity to Access Control: Use device identities to enforce role-based access control (RBAC). A temperature sensor, for example, should only have permission to send temperature data and receive firmware updates, not access other systems. This limits the potential damage if a device is compromised, a key principle of security in embedded systems.
Trade-Offs and Failure Modes
The primary trade-off with a robust identity management system is operational overhead and complexity. Provisioning unique identities during manufacturing adds cost and requires a secure process that can be difficult to manage with contract manufacturers. The infrastructure for managing a Public Key Infrastructure (PKI) and CLM is also significant. A failure in the certificate authority (CA) or revocation service can render an entire fleet of devices unable to connect. For low-cost, high-volume consumer gadgets, the expense of a secure element and the associated infrastructure might be considered prohibitive, leading teams to opt for less secure, symmetric key-based methods that are more vulnerable to cloning.
4. Regular Security Updates and Patch Management
An IoT device is only as secure as its most recent software version. Once deployed, devices become immediate targets for attackers who exploit newly discovered vulnerabilities. Regular security updates and a robust patch management process are essential for defending against these emerging threats. This is not just about pushing code; it’s a disciplined lifecycle of identifying, validating, deploying, and tracking updates to maintain device integrity and safety across a fleet.
This ongoing maintenance is one of the most critical IoT security best practices, particularly for products with long operational lifetimes. For example, a Medtronic insulin pump receiving an FDA-approved over-the-air (OTA) update can patch a critical security flaw without requiring a physical recall, protecting patient safety. Similarly, industrial PLCs from vendors like Siemens receive validated patches that prevent vulnerabilities from being used to disrupt manufacturing operations.
Key Insight: A “ship and forget” mentality is a critical failure in IoT security. Your product’s security is not a one-time achievement at launch; it is a continuous commitment to maintenance that must be designed into the architecture and supported for the device’s entire lifecycle.
Implementation Steps and Considerations
- Integrate an SBOM into CI/CD: Automatically generate a Software Bill of Materials (SBOM) and run vulnerability scans within your CI/CD pipeline. This provides immediate visibility into your software’s components and their known security issues.
- Design a Resilient OTA Mechanism: Build your OTA update process with cryptographic signature verification to confirm authenticity, compression to manage bandwidth, and reliable rollback support. If an update fails, the device must safely revert to its last known-good state.
- Establish Clear Communication Channels: Create a public security advisory channel and commit to a predictable patch release schedule, such as a monthly security bulletin. This builds trust with your users and partners.
- Implement Staged Rollouts: Deploy updates to a small percentage of devices first. Monitor device health and telemetry, and if no issues are detected, gradually expand the rollout. Automate rollback if key performance indicators degrade.
- Maintain Rigorous Audit Trails: For compliance and debugging, keep detailed logs of which devices received which update and when. This version tracking is non-negotiable for regulated industries like medical or aerospace.
Trade-Offs and Failure Modes
The primary trade-off of a robust update system is operational cost and complexity. Maintaining the infrastructure for building, signing, and delivering updates requires ongoing investment. There is also a risk of bricking devices in the field if an update fails catastrophically, making rollback and recovery testing vital. For air-gapped systems, the process becomes manual and labor-intensive, creating a lag in security posture. Finally, failing to get regulatory pre-approval for the update mechanism in safety-critical systems can block you from deploying even the most urgent security patches.
5. Network Segmentation and Access Control
A compromised IoT device should not be a backdoor to your entire network. Network segmentation prevents this by isolating devices into distinct security zones based on their function, trust level, and communication needs. By enforcing strict boundaries with firewalls, VLANs, and microsegmentation, this practice contains breaches and severely limits an attacker’s ability to move laterally from a low-value target to a high-value asset. It is a foundational principle for any secure IoT deployment.
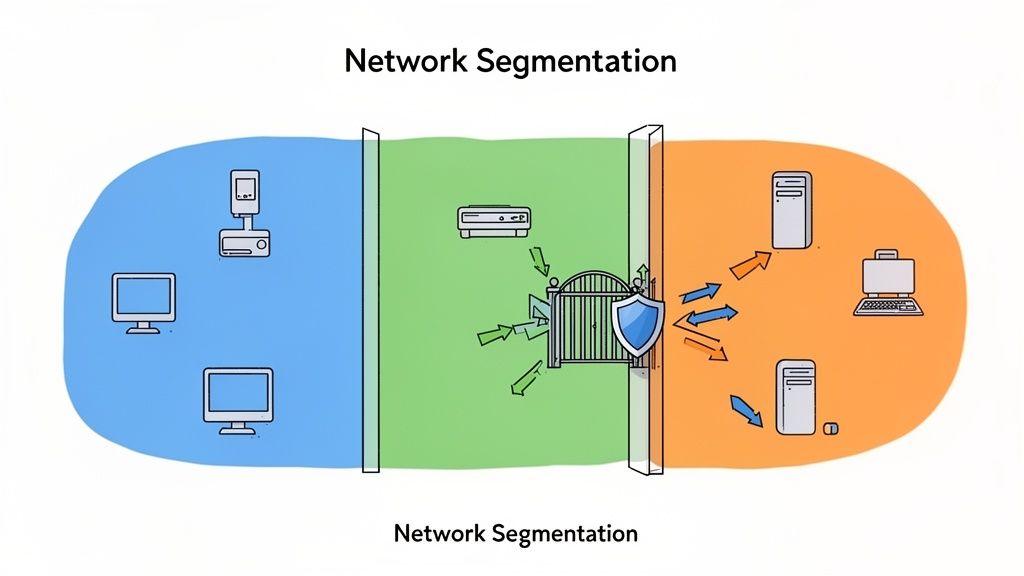
This control is indispensable in regulated and high-reliability environments. In a hospital, for instance, infusion pumps and patient monitors must be segregated from the guest Wi-Fi network and even from the primary IT infrastructure. Similarly, an industrial facility following the IEC 62443 standard uses a zone and conduit model to separate its control network from its business network, ensuring a breach on an enterprise system cannot halt production. This is one of the most critical IoT security best practices for maintaining operational integrity.
Key Insight: Network segmentation operates on a “guilty until proven innocent” model. It assumes a breach will occur and proactively builds walls to contain the damage, transforming a potential network-wide catastrophe into a manageable, isolated incident.
Implementation Steps and Considerations
- Design with Least Privilege: From the initial architecture phase, map all required data flows. Each device and segment should only be able to communicate with the specific endpoints necessary for its function. Deny all other traffic by default.
- Implement Network Access Control (NAC): Use a NAC solution to authenticate and authorize every device before it gains network access. NAC can enforce policies, checking for correct firmware versions or security configurations, and can automatically quarantine non-compliant devices.
- Layer Segmentation Technologies: Start with VLANs for broad logical separation. For high-sensitivity assets like industrial controllers or medical device gateways, apply micro-segmentation to create even smaller, more secure zones, sometimes isolating a single device.
- Encrypt Inter-Segment Communication: For any required communication that crosses segment boundaries, especially for remote access or cloud connectivity, use encrypted tunnels like VPNs or mutual TLS (mTLS) to protect data in transit.
- Monitor and Audit: Deploy tools that monitor traffic between segments and generate alerts for policy violations or suspicious activity. Regularly audit your segmentation rules to ensure they are still effective and document any approved exceptions.
Trade-Offs and Failure Modes
The primary trade-off of a segmented network is increased management complexity. Defining, configuring, and maintaining rules across firewalls and switches requires significant upfront effort and ongoing administration. Poorly configured rules can inadvertently block legitimate traffic, causing operational disruptions that are difficult to diagnose. To implement robust network segmentation and enforce strict security measures for your IoT devices, consider leveraging a managed Ethernet switch. A failure mode known as “rule bloat” can occur over time, where a complex and poorly documented set of rules becomes impossible to audit, creating hidden security gaps.
6. Secure Data Storage and Encryption at Rest
While network security protects data in transit, the information stored directly on an IoT device is equally vulnerable. Encryption at rest ensures that sensitive data on local storage-such as sensor readings, user credentials, or proprietary algorithms-remains unreadable even if an attacker gains physical access to the device or its memory components. This practice is a cornerstone of modern IoT security best practices, protecting against data breaches from stolen, lost, or improperly decommissioned hardware.
This is especially critical in regulated industries. A medical wearable like a glucose monitor must encrypt historical patient data to comply with HIPAA. Similarly, an industrial robot’s encrypted operational logs protect intellectual property, and an aerospace flight recorder’s encrypted sensor logs secure mission-critical information. Failing to encrypt data at rest creates a significant liability, turning a simple device theft into a major data breach.
Key Insight: Encryption at rest is a non-negotiable control for any device that stores sensitive information. It assumes a “zero trust” posture for the physical device itself, ensuring that even with full hardware access, an attacker cannot extract usable data.
Implementation Steps and Considerations
- Use Hardware-Backed Encryption: Whenever possible, employ System-on-Chip (SoC) features like hardware crypto accelerators (e.g., AES engines). These offload the computational work from the main CPU, minimizing performance impact on real-time operations and providing a more secure implementation than software-only libraries.
- Encrypt the Entire Filesystem: Instead of selectively encrypting certain files or database fields, which is prone to human error, implement full-disk or filesystem-level encryption. This guarantees that all data, including temporary files, logs, and crash dumps, is protected by default.
- Isolate Encryption Keys: The security of your encrypted data is only as strong as the protection of its keys. Store encryption keys in a hardware-based secure element, a Trusted Platform Module (TPM), or a processor’s secure enclave (like TrustZone). Never store keys in plaintext alongside the data they protect.
- Plan for Secure Decommissioning: Data’s lifecycle extends beyond the device’s operational use. When IoT devices are retired or repurposed, ensuring that any stored sensitive data is truly unrecoverable is a critical extension of data security. For the highest assurance in data destruction, organizations often look for expertise in technologies and standards like AAA NAID Certified Secure Asset Disposition.
Trade-Offs and Failure Modes
The primary trade-off is the performance overhead and system complexity. While hardware accelerators mitigate this, encryption still consumes CPU cycles and power, which can be a significant constraint for battery-powered devices. Key management also introduces complexity; a lost key can render all device data permanently inaccessible, making robust key backup and recovery procedures essential. A failure in the key-loading mechanism or a corrupted encrypted partition can “brick” a device in the field, requiring physical recall and repair. For extremely cost-sensitive consumer electronics, the bill-of-materials cost for a TPM or a more capable SoC may be a barrier.
7. Input Validation and Secure Coding Practices
The software running on an IoT device is the attacker’s primary target. Vulnerabilities like buffer overflows, injection attacks, and logic errors are common entry points. Implementing rigorous input validation and adhering to secure coding standards from the outset is a critical practice for building resilient systems. This isn’t just about patching bugs; it’s about fundamentally architecting software to resist entire classes of attacks before they can be exploited.
For high-reliability products, this discipline is non-negotiable. A medical device that improperly parses incoming data could malfunction with severe patient safety consequences. Similarly, industrial control systems must validate every command and protocol message to prevent operational failure or sabotage. Adopting a secure software development lifecycle (SSDLC) is a core component of any serious IoT security best practices framework.
Key Insight: Most software vulnerabilities stem from a single root cause: making incorrect assumptions about external data. Secure coding and input validation are disciplines designed to treat all external input as hostile until proven otherwise, preventing attackers from violating those assumptions.
Implementation Steps and Considerations
- Establish and Enforce Coding Standards: Early in the project, adopt and mandate a secure coding standard like MISRA C/C++, CERT, or the CWE Top 25. These standards provide clear, actionable rules for avoiding common pitfalls in memory management, data handling, and control flow.
- Integrate Static Analysis (SAST): Embed SAST tools (e.g., SonarQube, Coverity) into your continuous integration (CI) pipeline. Configure the pipeline to fail the build if new, high-severity security violations are introduced, making security a non-negotiable quality gate.
- Mandate Security-Focused Code Reviews: Every code change must be reviewed by at least one peer trained in security. Reviewers should specifically look for common vulnerabilities, logic flaws, and deviations from the established coding standard.
- Perform Fuzz Testing: Actively fuzz all untrusted data inputs, including network protocols, user interfaces, and file parsers. This automated testing technique feeds malformed data to your code to uncover hidden crashes and security holes that standard testing might miss.
Trade-Offs and Failure Modes
The most significant trade-off of a rigorous SSDLC is the upfront investment in time, tools, and training. Development velocity may seem slower initially as engineers adapt to stricter standards and review processes. Without strong management buy-in, developers may be pressured to bypass SAST checks or conduct superficial code reviews to meet deadlines, accumulating security debt. The main failure mode is inconsistent application; if secure coding is treated as an optional checklist item rather than an architectural principle, critical vulnerabilities will inevitably slip through into production.
8. Monitoring, Logging, and Threat Detection
An IoT device that operates silently in the field is a blind spot. Without a clear view of its behavior, you can’t distinguish normal operation from a security incident. Comprehensive monitoring and logging provide the necessary visibility to detect anomalies, investigate intrusion attempts, and conduct post-breach forensics. This practice involves systematically recording device behavior, system events, and security-relevant activities to enable continuous threat detection and response.
This ongoing vigilance is a critical part of a mature IoT security posture. For example, a hospital’s network of infusion pumps must have detailed audit logs to comply with HIPAA and to investigate any unauthorized changes that could affect patient safety. Similarly, industrial control systems rely on real-time monitoring to detect behavior that might signal a cyber-physical attack, preventing costly downtime or equipment damage. Centralized logging and analysis turn raw data from thousands of endpoints into actionable security intelligence.
Key Insight: You cannot defend what you cannot see. Effective monitoring and logging are the sensory system of your IoT deployment, providing the ground truth needed to detect threats, respond to incidents, and satisfy regulatory audit requirements. It moves security from a passive, one-time setup to an active, ongoing process.
Implementation Steps and Considerations
- Design Logging from the Start: Logging should be an architectural requirement, not an afterthought. Define critical events early, including authentication attempts (success and failure), configuration changes, firmware updates, and authorization failures.
- Centralize and Secure Log Ingestion: Devices should ship logs to a centralized, secure system in near real-time. Relying on local storage is risky, as logs can be tampered with or lost if a device is compromised or fails. Use platforms like the ELK Stack, Splunk, or cloud-native services like AWS CloudWatch and Azure Monitor.
- Sanitize All Log Data: Be extremely careful to avoid logging sensitive data like credentials, API keys, or personally identifiable information (PII) in plain text. Implement robust masking and sanitization routines to protect data privacy and reduce the impact of a log repository breach.
- Establish Alerting Baselines: Configure your security information and event management (SIEM) system to generate alerts based on known attack signatures and deviations from normal operational baselines. Machine learning-based tools like Azure Sentinel can help identify subtle anomalies that rule-based systems might miss.
- Define and Enforce Log Retention Policies: Determine your log retention requirements based on regulatory mandates and operational needs. For medical or aerospace, this can be several years. Ensure logs are stored immutably to maintain a verifiable audit trail.
Trade-Offs and Failure Modes
The biggest trade-offs are cost and performance. Transmitting, processing, and storing massive volumes of log data can be expensive, especially for large-scale deployments. On resource-constrained devices, extensive logging can consume precious CPU cycles, memory, and battery life, potentially impacting the primary function of the device. A failure in the logging pipeline, or “alert fatigue” from poorly tuned rules, can render the entire system ineffective, creating a false sense of security while actual threats go unnoticed.
9. Secure Configuration Management and Hardening
Every feature, service, and open port on an IoT device represents a potential attack surface. Secure configuration management and hardening is the disciplined practice of minimizing this surface by establishing a secure baseline, disabling unnecessary components, and enforcing strict access controls. Attackers often rely on finding devices with default credentials, unused-but-vulnerable services, or open debug ports. A hardened configuration is a critical, proactive defense against these low-effort, high-impact attacks.
This practice is non-negotiable for large-scale or critical deployments where manual oversight is impossible. For instance, a fleet of industrial robots shipped with an active SSH daemon and default password becomes an easy target for network-based attacks. Likewise, a medical device with an exposed JTAG or serial console port could allow an attacker with physical access to dump firmware and extract sensitive credentials or intellectual property. Hardening ensures devices are shipped in a “least privilege” state.
Key Insight: Default configurations are designed for developer convenience, not production security. Hardening flips this script by creating a “deny-by-default” posture, where only explicitly required and validated services are permitted to run. It’s one of the most effective IoT security best practices for reducing the attack surface.
Implementation Steps and Considerations
- Establish a Secure Baseline: Do not start from a vendor’s default image. Use industry-recognized hardening guides like the CIS Benchmarks or DISA STIGs as a foundation. Create a custom, minimal base image that includes only the libraries, packages, and services essential for your application.
- Automate and Version Control Configurations: Treat your configurations as code. Store firewall rules, service settings, and user account policies in a version control system like Git. Use automation tools (e.g., Ansible, Puppet) to apply these baselines consistently during manufacturing and updates.
- Disable All Unnecessary Interfaces: This includes both physical ports (JTAG, UART/serial, USB) and network services (Telnet, FTP, non-TLS HTTP). If a debug port is needed for manufacturing or field service, it must require strong authentication before activation.
- Enforce Strong Credential Policies: Completely remove or disable all default vendor accounts. If local accounts are required, enforce strong, unique passwords that are provisioned securely during manufacturing. Never use hardcoded credentials in firmware.
- Implement Configuration Drift Detection: A device’s configuration can “drift” from its secure baseline due to field updates, operator error, or malicious activity. Implement a mechanism, either on-device or via a central server, to periodically check configuration integrity and alert on any unauthorized changes.
Trade-Offs and Failure Modes
The main trade-off of aggressive hardening is the potential impact on field serviceability and debugging. If a device in the field fails, a disabled debug port can make root cause analysis extremely difficult and costly, sometimes requiring the unit to be returned. This creates tension between security and operations. A balanced approach might involve a secure, authenticated mechanism to temporarily enable diagnostic access. Another challenge is maintenance; as your software evolves, your hardened baseline must be continuously updated and re-validated, which adds process overhead to your secure development lifecycle.
10. Privacy by Design and Data Protection
In regulated industries like healthcare and critical infrastructure, security and privacy are not optional add-ons; they are core product requirements. Privacy by Design is a framework that embeds data protection principles into the entire product development lifecycle, from the initial architecture to end-of-life. Instead of treating privacy as a compliance checkbox to be ticked before launch, this approach forces teams to proactively address how user data is collected, processed, stored, and deleted. This is fundamental for building user trust and ensuring compliance with stringent regulations like GDPR and HIPAA.
Forgetting this principle can lead to costly redesigns, regulatory fines, and permanent brand damage. A medical device that over-collects patient data or a smart utility meter that lacks clear consent mechanisms creates significant legal and ethical risks. Integrating privacy from the start is one of the most critical IoT security best practices for avoiding these pitfalls and building systems that respect user rights by default.
Key Insight: Privacy is not the same as security. Security protects data from unauthorized access, while privacy dictates what data is collected and how it is used in the first place. A perfectly secure system can still be a privacy nightmare if it collects unnecessary information.
Implementation Steps and Considerations
- Conduct a Privacy Impact Assessment (PIA): Early in the design phase, perform a PIA to map out all data flows. Document what personal data is collected, why it’s needed, where it’s stored, and who has access. This identifies privacy risks before a single line of code is written.
- Embrace Data Minimization: Adhere to the principle of collecting only the data absolutely necessary for the device’s stated function. Avoid the temptation to gather extra data “just in case” it becomes useful later. This reduces your liability and the potential impact of a data breach.
- Automate Data Lifecycle Management: Implement automated policies for data retention and deletion. For instance, a system should automatically purge user data after a defined period or upon user request, ensuring compliance with regulations like GDPR’s “right to be forgotten.”
- Build Transparent User Controls: Provide users with clear, granular controls over their data. This includes easy-to-understand consent forms for specific features (opt-in, not opt-out), a dashboard to view collected data, and a simple process to export or delete their information.
Trade-Offs and Failure Modes
The main trade-off of Privacy by Design is the upfront investment in planning and engineering. It requires more rigorous design documentation, potentially more complex software to handle granular consent and data management, and can limit future business models that rely on broad data analysis. For example, implementing on-device processing to avoid sending sensitive data to the cloud may require a more powerful and expensive microcontroller. A common failure mode is “privacy theater,” where a company has a detailed privacy policy but lacks the technical enforcement to back it up, leading to a major gap between promises and reality.
A Realistic Scenario: Securing a Remote Patient Monitoring Device
The Problem: A startup is in the EVT (Engineering Validation Test) phase for a new remote vital signs monitor. They are under pressure to get to DVT (Design Validation Test) within three months to meet investor milestones. The device collects patient ECG and SpO2 data and transmits it to a cloud platform for clinician review. The engineering team consists of two hardware engineers and three firmware developers. They have focused on core functionality but have accumulated significant security debt.
The Decision: The CTO must decide on a minimum viable security architecture that can be implemented without derailing the schedule but is robust enough for future HIPAA compliance and a 510(k) submission.
Criteria & Recommendation:
- Device Integrity (High Priority): Implement Secure Boot (#1) using the SoC’s built-in capabilities. Even if full chain-of-trust is deferred, ensuring the primary application is signed is non-negotiable.
- Data Protection (High Priority): Implement End-to-End Encryption (#2) using mTLS for all device-to-cloud communication. Use the platform’s secure element to store the device’s private key. Encrypt patient data on the device’s flash storage (#6).
- Access Control (Medium Priority): Provision unique Device Identities (#3) during manufacturing test. Defer complex role-based access for now but ensure no two devices share an identity.
- Maintainability (Lower Priority for DVT): Build the hooks for a Secure OTA (#4) mechanism but defer full backend implementation until after the DVT build, focusing first on a secure in-field provisioning process.
Risks & Outcome: This prioritized approach accepts the risk of a less-than-perfect OTA process in the short term to focus on the unrecoverable architectural decisions: hardware-backed identity and encryption. This allows the team to pass DVT with a defensible security posture, satisfying immediate technical and business goals while creating a solid foundation for future hardening and compliance efforts before mass production.
Your Monday-Morning Next Steps: Turning Best Practices into Action
The list of IoT security best practices can feel overwhelming. The goal is not to implement every control perfectly on day one but to build a resilient, defensible system where security is a measurable outcome of your engineering process.
- Establish Ownership: Assign a security champion—a lead engineer or program manager—responsible for tracking security requirements and ensuring they are not deprioritized.
- Start with a Threat Model: Before finalizing the schematic, conduct a threat modeling exercise using a framework like STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) to identify and prioritize the most significant risks for your specific product.
- Integrate into Your Product Lifecycle: Embed security into your development gates. Make a passing SAST scan a requirement for code check-in. Add security test cases to your DVT plan. Make a secure boot validation part of your manufacturing test sequence.
Operational Insight: Waiting until DVT to address fundamental security issues like secure boot or device identity is a recipe for major schedule delays and costly hardware respins. A root-of-trust that is not designed in from the start is nearly impossible to add later without completely re-architecting your system. This is a common failure pattern we see in program rescue engagements.
Mastering these IoT security best practices creates a powerful competitive advantage. It demonstrates a commitment to quality and reliability that builds trust with customers and regulators and protects the long-term value of your connected product ecosystem.
Ready to assess your current security posture against these IoT security best practices? Sheridan Technologies offers an IoT Security Architecture Consult to help you identify gaps, prioritize risks, and build a production-ready security roadmap. Our integrated expertise across hardware, firmware, and manufacturing ensures your security strategy is both robust and realistically implementable.
